06/17: Geraldさんの基調講演@SFUS25

Sharkfest ’25 US 始まりました! Geraldさんの基調講演とStoratosharkの話やコアデベロッパーの紹介と進みます。また、今年はStratosharkやWCA試験などの話題もありました。https://sharkfest.wireshark.org
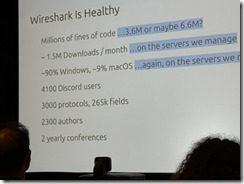
3000プロトコル 265000フィールド
360万行(660万行)のコードへと成長しました。

Wireshark開発者会議 Sharkfest ’25 US バージニア州リッチモンドにて開催されます!また、新しいWiresharkの認定試験WCA(Wireshark Certified Analyst)も始まります。

Sharkfest公式は https://sharkfest.wireshark.org/
WCA試験は https://www.wireshark.org/certifications
06/06: Wireshark4.4.7

Wireshark4.4.7がリリースされました。
主な変更はCVE-2025-5601のダイセクタのクラッシュ、パケットダイアグラムでビット位置の誤り、WobSocketにおいて2番目のメッセージが展開できない、Luaダイセクタ、CIGI、ZigBee、LDAP、Bluetoothプロトコル等の修正です。

InteropTokyo Best of Show Awardを受賞したパケキャプアプライアンスIOTAの最上位モデル「IOTA 100 Core」が登場します!ついに念願の100Gbpsのノンサンプリング・フルキャプチャが実現します。 
キャプチャ性能はついに
FPGAキャプチャ持続書込最大100Gbps
解析スループット平均100Gbps
同時フロー最大 900万フロー/秒
パケット最大 1,600万パケット/秒を実現
取得したパケットは
307TBのRAID5ストレージにフルレートのパケットを
保存・メタデータ化するとともに解析し
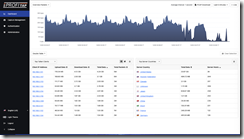
Grafanaなダッシュボードで見える化を行います
詳細は https://www.ikeriri.ne.jp/develop/profitap/iota100gcore.html
02/20: Wireshark4.4.4リリース
Wireshark4.4.4がリリースされました。
主な変更はwnpa-sec-2025-01等のセキュリティ対応、表示フィルタがアクティブな際に列ソート、統計>対話画面でTCPタブ外をクリック、Windows環境でAndroidのextcapプラグインが2秒間パケットない等で失敗する問題、DNSをはじめとするダイセクタ修正になります。
ダウンロードは https://www.wireshark.org/download.html
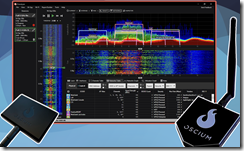
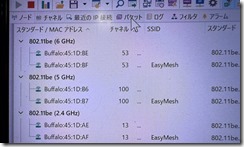
02/06: 2.4/5/6GHz スペアナ Wi-Spy Lucid
OSCIUM社がMetageek社を取得したことによりWiPry ClarityはWi-Spy Lucidにリブランディングされ、 6GHzのスペアナのWi-Spy Lucidと対応したChanalyzer5ベースのもうひとつのChanalyzerと指向性アンテナをセットにしたバンドル版が登場します
11/21: Wireshark4.4.2リリース
Wireshark4.4.2がリリースされました。主変更はTCPサーバーポートでダイセクタが選択されない場合クライアントポートを基準にプロトコルが選択される動作が廃止されました。(アクティブFTP20番ポートを除きます)このデフォルト動作は設定で変更できます。
tshark -Gにて設定を行う記述は tshark -G fields, prefixの記述となりました。
また、wnpa-sec-2024-14や、wnpa-sec-2024-15などの脆弱性対応があげられます。
POP3、IEEE802.11beなどのダイセクタ修正などがあります。
wnpa-sec-2024-14/15の脆弱性対応に加え macOS15.0でiPhoneミラーリング切断 POP3エラーメッセージ WiFiの256ビットブロックACK ポータブル版でのExtcap フィルタやLuaでの浮動小数点動作の修正 tsharkでキャプチャフィルタ設定した場合のクラッシュ問題等も修正されています。
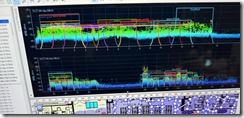
11/06: Profitap社ブース@Sharkfest'24EU

いけりり@Wireshark開発者会議Sharkfest'24EUです。
  
  いけりりはProfitap社代理店として、オールインワンキャプチャ機器のIOTAやProfiSharkシリーズを長く取り扱っております。
長いProfitap社との信頼関係から、安価にそして、迅速にサポートを提供できます。
ぜひお問い合わせくださいませ。→いけりり Profitap社ページ https://www.ikeriri.ne.jp/develop/profitap/iota.html

いけりり@Sharkfest'24Europe始まりました!
今年のバッジやきっとはこんな感じです。 
Geraldさんの基調講演が始まっています。
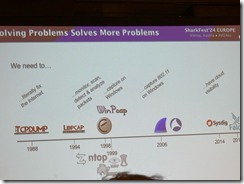
WiresharkもFalcoヤSysdig統合でなんでもアナライザへと向かっています
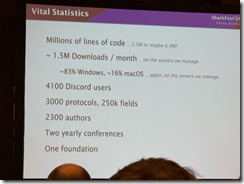
ソースコードは整理して350万行、3000プロトコル、25000フィールドとまだまだ広がっていきます