[Information on examples of open courses for customers sponsored by Ikeriri]
Introducing recent examples of corporate events.
|
NEWS Added examples of recent courses held. (2023/01)
Ikeriri has been holding open seminars for over 15 years.
Focusing on Wireshark and Kali Linux, we develop cybersecurity-related
Python/Lua/Java/C++/C#/.NET, as well as information processing engineer exam preparation,
vendor exam preparation (Cisco/Oracle/Microsoft/CompTIA/eCouncil), etc.
→Past Open Seminars →Wireshark Track Record →Cyber security track record
→Information Processing Engineer Exam Vendor exams, etc.
We also support other themes and customizations, so please contact us. |
 |
| Seminar name/code |
Time/venue/price example |
Overview |
Details |
Introduction to Penetration Testing by BadUSB
(Code:BadUSB-1)
|

1 day (10:00-18:00)
At our training center or your site
¥27,500 per person/1 day
and equipment costs separately |
BadUSB will be happy to actually conduct a penetration test using Hak5's USB Rubber Ducky.
The purpose is to enable in-house penetration testing using BadUSB devices.
|
1 day
(10:00-18:00)
Introduction to penetration testing with BadUSB devices Details
 |
| Seminar name/code |
Time, venue, price |
Overview |
Details/Application |
[Lua-1]
Introduction to Lua scripts and
Wireshark
customization
|

1 day (10:00-18:00)
At our training center or your site
¥27,500 per person/1 day (tax included)
|
Learn the specifications of
Lua scripts used in Wireshark's disector,
listener, etc. and
programming in Wireshark.
Especially for Wireshark, you will learn
writing plug-ins such as disectors and listeners,
adding functions to Wireshark,
and how to analyze unknown protocols
. |
1 day
(10:00-18:00)
Lua scripting and
Wireshark customization
Getting started details
 |
| Seminar name/code |
Time/venue/price example |
Overview |
Details |
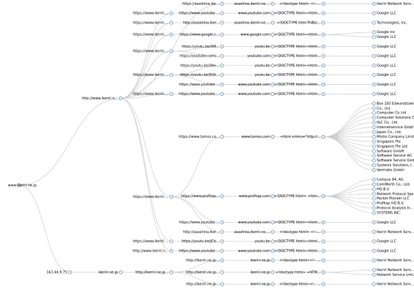
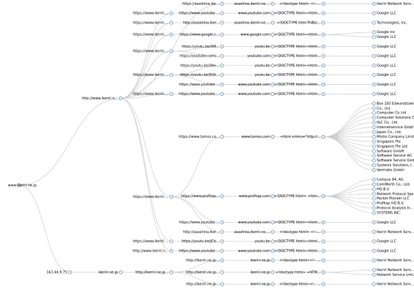
[OSINT-1]
Introduction to OSINT
Using OSINT
Collection and analysis of threat information
|
2 days (10:00-18:00)
or 3 days including SNS tracking
At our training center or your site
¥27,500 per person/1 day
|
Collection of threat information using OSINT (open source intelligence)
Organization/individual tracking method
SNS (Twitter/Facebook, etc.) tracking
Malware analysis method using OSINT
APT group investigation |
2 days
(10:00-18:00)
or
3 days
(SNS detailed investigation included)
OSINT FundamentalsSeminar
Details
 |
| Seminar name/code |
Time/venue/price example |
Overview |
Details |
[OSINT-2]
OSINT systemization
OSINT information integration
System usage
|

1 day (10:00-18:00)
or 2 days including system construction
At our training center or your site
¥27,500 per person/1 day
|
Collection of threat information using OSINT
Aggregation of threat information and malware information
Building a threat intelligence platform
Build a threat intelligence platform by automating the collection of threat information using OSINT (open source intelligence). Creates a database of threat information and malware information and makes it searchable |
1 day
(10:00-18:00)
or
2 days
(construction included)
OSINT Systemization
Details
 |
| Seminar name/code |
Time/venue/price example |
Overview |
Details |
[OSINT-4]
MISP
OpenCTI
Construction and Utilization
|

3 days (10:00-18:00)
At our training center or your site
¥27,500 per person/1 day
|
Collection of threat information using OSINT
Aggregation of threat/malware information Build integrated system
Build MISP (virtual machines and containers)
Build OpenCTI (containers)
Initial settings of MISP, event registration, server synchronization, synchronization of specified servers and content (PUSH/PULL)
Configuring and importing external feeds
Update and management
Building OpenCTI (container)
Overview of initial setup and operation of OpenCTI
Connector configuration and import
Update and management
vinegar |
3 days
(10:00-18:00)
(construction included)
MISP
OpenCTI
Building and leveraging
Details
 |
| Seminar name/code |
Time/venue/price example |
Overview |
Details |
[OSINT-5]
MISP/OpenCTI Chrome original
Function extension development
|

3 days (10:00-18:00)
At our training center or your site
¥27,500 per person/1 day
|
1. Basics of Chrome extension development
2. Registration process using MISP REST API
3. Registration process using OpenCTI REST API
4. Design and development of your own extension |
3 days
(10:00-18:00)
(construction included)
MISP/OpenCTI Chrome original
function extension development
Details
 |
| Seminar name/code |
Time/venue/price example |
Overview |
Details |
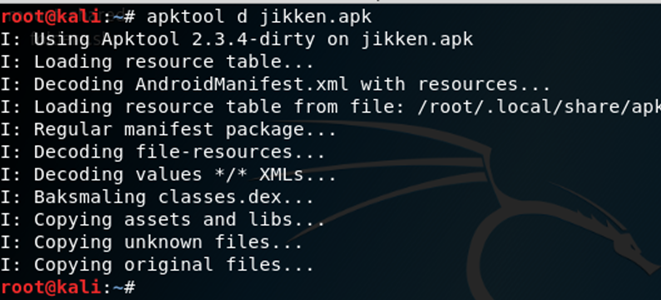
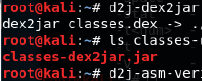
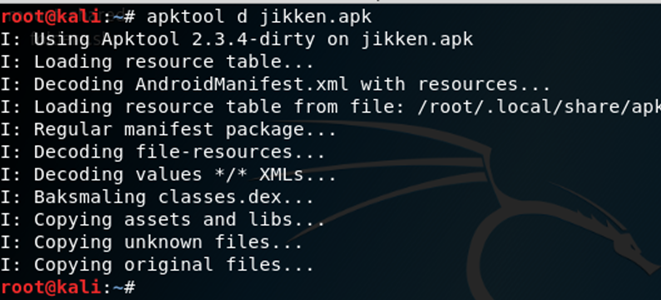
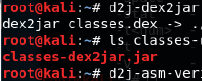
[Malware-5]
AndroidMalware
static analysis Seminar
|
1 day (10:00-18:00)
or 3 days from Java basics
At our training center or your site
¥27,500 per person/1 day
|
Static analysis of Android Malware. Perform static analysis of
using the
decompiler using the RAT type
apk, Sagawa.apk and
AgentSmith by
nsfvenom as examples.
For those who have completed Java/Android
Starting with Java basics, we will move on to
Java basics, java.net and
Android applications
in three days. |
1 day
(10:00-18:00)
or
3 days
(from Java)
Android Malware
Static Analysis Seminar
Details
 |
| Seminar name/code |
Time/venue/price example |
Overview |
Details |
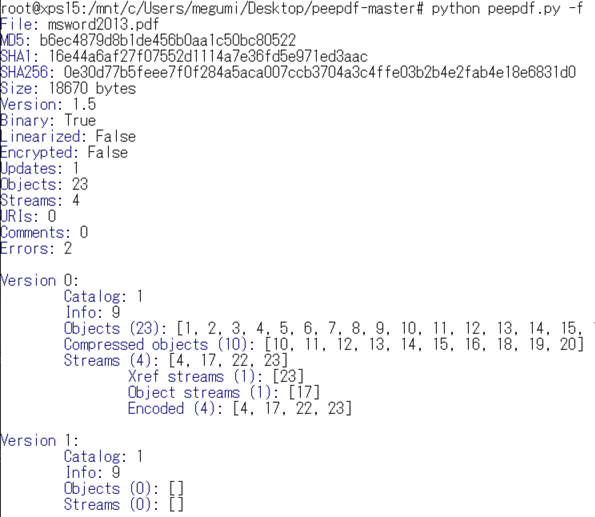
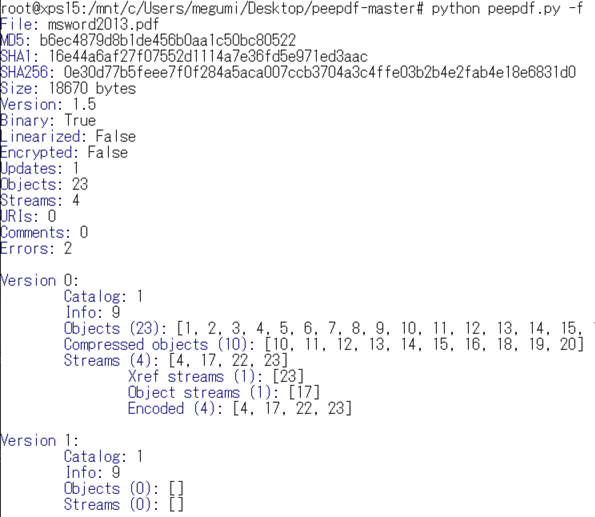
[Malware-4]
File structure
Analysis seminar
|
1 day (10:00-18:00)
At our training center or your site
¥27,500 per person/1 day
|
Understand the header/body and structure of each file (executable file, image, video, audio, document file, etc.) in binary data.
Learn about key file structures using binary editors, scripts, and analysis tools.
Analyzes the structure of Office formats, PDFs, text files, audio, videos, images, and system files.
|
1 day
(10:00-18:00)
File structure
Analysis seminar details
 |
| Seminar name/code |
Time/venue/price example |
Overview |
Details |
[Malware-3]
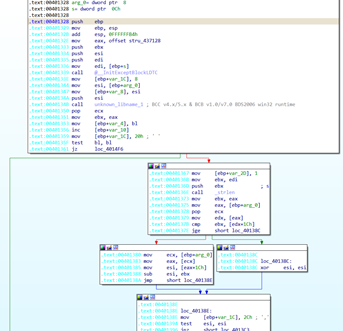
Hex-Ray Introduction to static analysis of Malware using IDAPro
and WinDbg
|
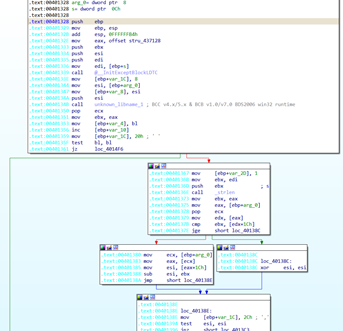
2 days (10:00-18:00)OR3 days
At our training center or your site
JPY 27,500 per person/1 day
|
This is a Malware reverse engineering seminar using IDA Pro and WinDbg.
Using IDA Pro and WinDebug, we disassemble the EXE and DLL of Windows (PE format 32-bit/64-bit format) and statically analyze the behavior of Malware.
Learn the basics of how to use the x86 assembler and debugger, and how to track binaries. |
2 days
(10:00-18:00)
Malware static analysis using Hex-Ray IDAPro
and WinDbg
 |
| Seminar name/code |
Time/venue/price example |
Overview |
Details |
[Malware-2]
Introduction to Malware Analysis and Forensics with Kali
|
1 day (10:00-18:00)
At our training center or your site
¥27,500 per person/1 day
|
Learn the basics of malware analysis and digital forensics by utilizing dynamic analysis, static analysis, and forensic tools included in Kali Linux.
Examining Windows and Linux programs and memory/obtaining memory dumps
Learn the flow of malware analysis by utilizing open source tools included in Kali Linux to acquire malware, surface analysis, dynamic analysis, and static analysis without using expensive commercial products.
Manipulate Windows/Linux/Android disk images and memory dumps and use digital forensic tools to analyze the contents, verify operations, confirm information, and restore data.
|
1 day
(10:00-18:00)
Learn more about Introduction to Malware Analysis and Forensics with Kali
 |
| Seminar name/code |
Time/venue/price example |
Overview |
Details |
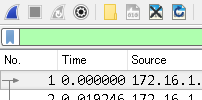
[Malware-1]
Introduction to Malware analysis using packet capture
|
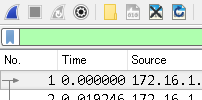
1 day (10:00-18:00)
At our training center or your site
¥27,500 per person/1 day |
This is an introductory seminar on Malware analysis using packet capture, where you can check out the method and analysis of malware using packet capture by actually using Wireshark.
We will use Wireshark, a LAN analyzer, to analyze the operation and behavior of malware, as well as introduce methods for collecting information, discovering root causes, and creating incident reports.
This is an introductory seminar on malware analysis using packet capture. Using Wireshark, a LAN analyzer, we will analyze the operation and behavior of malware, as well as introduce methods for collecting information, discovering root causes, and creating incident reports. *We will use capture files (trace files) from overseas Wireshark developer conferences, etc.
|
1 day
(10:00-18:00)
Details on Introduction to Malware Analysis with Packet Capture
 |
| Seminar name/code |
Time/venue/price example |
Overview |
Details |
[Python-10]
Python
for building OSINT system
|
5 days (10:00-18:00)
At our training center or your site
¥27,500 per person/1 day
|
Beginners will learn the Python skills necessary to build OpenCTI and MISP for OSINT systemization, and to acquire and process customized data. |
5 days
(10:00-18:00)
Python for building an OSINT system
 |
| Seminar name/code |
Time/venue/price example |
Overview |
Details |
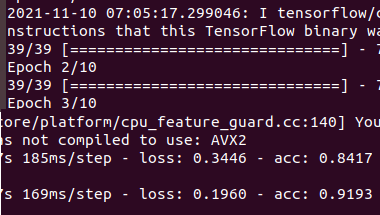
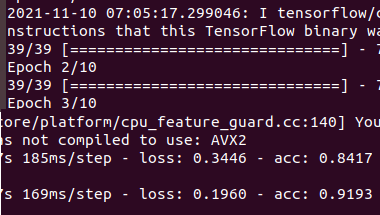
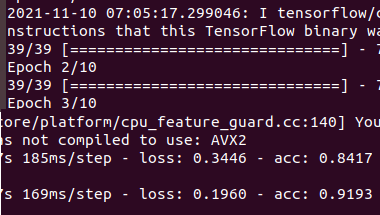
[Python-2]
Malware analysis automation using Python
|
2 days (10:00-18:00)
At our training center or your site
¥27,500 per person/1 day
|
Enables more efficient malware analysis using Python.
Leverage AI to build your own malware detector using the machine learning libraries scikit-learn and Keras. |
2 days
(10:00-18:00)
Malware analysis automation using Python
 |
| Seminar name/code |
Time/venue/price example |
Overview |
Details |
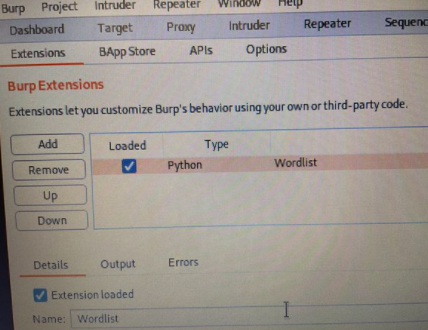
[Python-1]
Python for penetration testing
|
2 days (10:00-18:00)
At our training center or your site
¥27,500 per person/1 day
|
It allows you to create a Python environment, install and update packages, switch environments, use libraries, and check APIs in Windows/Kali Linux environments.
Learn the basics of creating security tools by writing Python scripts.
Enables you to create cybersecurity tools using Python code and libraries.
|
2 days
(10:00-18:00)
Python for penetration testing for penetration testing |
| Seminar name/code |
Time/venue/price example |
Overview |
Details |

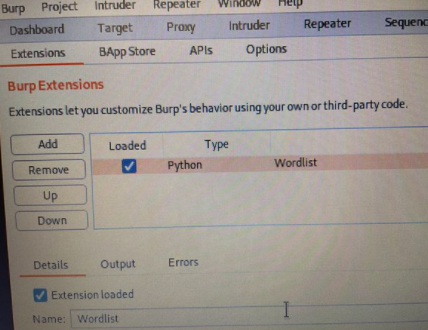
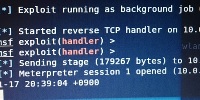
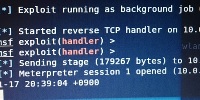
[Kali-1]
Introductory seminar on cybersecurity using Kali Linux
|
1 day (10:00-18:00)
At our training center or your site
¥27,500 per person/1 day |
for penetration testing
Linux distribution
with Kali Linux
Cybersecurity introductory seminar
for penetration testing
Fundamentals of CLI operation
Port scanning
System vulnerability testing
System penetration
Verify attacks and defenses such as privilege escalation
Remote control of smartphones
through practical training
and learn countermeasures against them
The lecturer will explain it on screen, but if you can see the packets with Wireshark, you will understand better
|
1 day
(10:00-18:00)
Introduction to Kali Linux
Seminar details
 |
| Seminar name/code |
Time/venue/price example |
Overview |
Details |

[Kali-2]
Cyber security application seminar using Kali Linux
|

1 day (10:00-18:00)
At our training center or your site
¥27,500 per person/1 day |
For penetration testing
Linux distribution
with Kali Linux Cyber security application seminar
How to examine logs and settings with Linux CLI
How to examine programs
Password cracking
(offline/online)
MAC address spoofing,
MitM (man-in-the-middle) attacks
Spoofing
DoS/DDoS attack
Website vulnerability investigation
Wireless LAN investigation and attack/intrusion
Confirm attacks and defenses such as
through practical training and learn
countermeasures.
The lecturer will explain it on screen, but if you can see the
packet with Wireshark, you will understand
better.
|
1 day
(10:00-18:00)
Kali Linux Application
Seminar Details
 |
| Seminar name/code |
Time/venue/price example |
Overview |
Details |
[USB-1] USB Pen Test Tool/Hardware Security Equipment Utilization and USB Analysis Forensic Seminar
|

1 day (10:00-18:00)
At our training center or your site
¥27,500 per person/1 day
*Negotiable depending on distributed equipment
|
This is an introductory seminar on USB frame analysis and USB forensics using Wireshark, including the use of USB pen test tools and hardware security devices such as keyloggers/attack intrusion tools.
|
1 day
(10:00-18:00)
Hardware
Security Equipment
USB Pen Test
Seminar Details
 |
| Seminar name/code |
Time/venue/price example |
Overview |
Details |
Spectrum
Analyzer WiSpy
and Chanalyer
AP Discovery - Tool
by InSSIDer Wireless LAN Trouble
Shooting |
Half day (14:00 pm
-17:30)
At our training center or your site
¥27,500 per person/1 day
|
We mainly troubleshoot problems such as disconnected, unconnected, or slow wireless LANs by analyzing the physical layer.
Use the AP detection tool InSSIDer for Office to check for identical CHs and CHs with overlapping spectra and measure throughput.
Confirm foreign waves and channel utilization using spectrum analyzers WiSpyDBx and Chanalyzer5. |
Half day
(14:00-17:30)
Wireless LAN troubleshooting details with spectrum analyzer WiSpyChanalyer and AP detection tool InSSIDer

|
| Seminar name/code |
Time/venue/price example |
Overview |
Details |
[Wireshark-1]
by Wireshark
Packet capture
introductory seminar
You can see and understand more of the packets flowing through the network with Wireshark. |
New book
Wireshark2.x compatible
1 day (10:00-18:00)
At our training center or your site
¥27,500 per person/1 day
|
In addition to reviewing the basics of network protocols and architecture, you will learn by actually observing encapsulation, decapsulation, and TCP/IP packets.
How Wireshark works
Packet captureSetup
Display filter/capture filter
Includes Wireshark customization/TIPS
Learn network analysis techniques while actually capturing packets and analyzing dumps using the open source LAN analyzer Wireshark
*Our introductory seminars are mainly for NIer and SI students
, and the content may be difficult for individuals
. The content is a bit complicated and requires knowledge of TCP/IP and command operation.
This is a series of
seminars that include Wireshark techniques and tips. Even for advanced users, we recommend taking
in conjunction with Applied/Radio. |
1 day
(10:00-18:00)
Introduction to Wireshark
Seminar Details
 |
| Seminar name/code |
Time/venue/price example |
Overview |
Details |
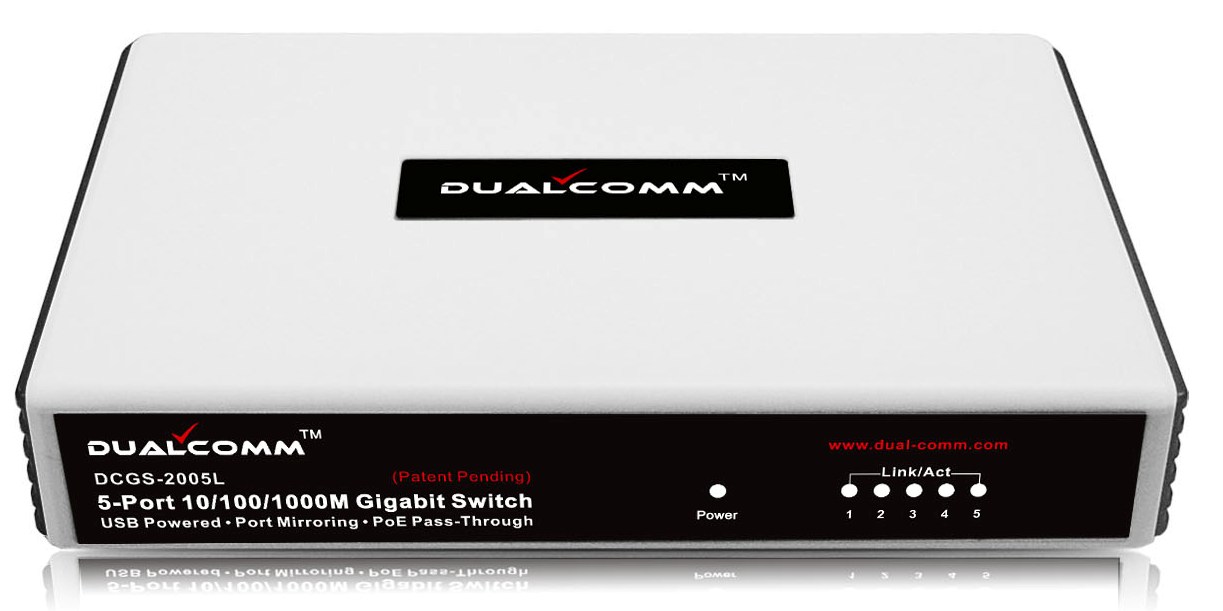
[Wireshark-9]
LAN analyzer
Packet capture by Wireshark
Trend analysis application

10/100Mbps USB TAP
10/100/1000Mbps Supports additional distribution of USB TAP
|
A new book is out!

1 day (10:00-18:00)
At our training center or your site
¥27,500 per person/1 day |
Learn the latest Wireshark tips and techniques that can be used in practice
Difference between tapping and spanning
Catch up on the latest version of Wireshark
Wireshark customization TIPS
Application of display filters and capture filters tshark/mergecap/editcap etc.
Batch processing and JSON processing with CLI
TCP application analysis
UDP application analysis
Anomaly analysis using Wireshark
SSL/TLS decryption
Teaching the latest Wireshark know-how
We highly recommend taking this course as a set with the introductory course. |
1 day
(10:00-18:00)
Wireshark Application
Seminar Details
 |
| Seminar name/code |
Time/venue/price example |
Overview |
Details |
[Wireshark-7]
Wireless LAN spectrum + packet analysis and security seminar using AirPcap + Wi-Spy |

1 day (10:00-18:00)
At our training center or your site
¥27,500 per person/1 day)
|
Practical
Wireless LAN (IEEE802.11) Packet
Capture and Spectrum Analysis Seminar
2.4GHz (/5GHz) spectrum analysis, wireless LAN throughput measurement, packet capture, IEEE802.11 dump analysis, WLAN visualization and analysis method, WPA1/2 encryption and decryption using Wireshark4・Learn security and troubleshooting through practical training and acquire wireless LAN analysis techniques that can be put to practical use.
The physical layer uses Wi-Spy/inSSIDer to check the spectrum and analyze foreign waves and interference.
At the data link layer, you will use packet capture dongles such as AirPcap/EyeP.A./npcap/aircrack-ng to actually acquire IEEE802.11 frames with Wireshark, and learn about wireless LAN operations and troubleshooting through dump analysis and visualization.
For security, you will learn the structure and protection of wireless LAN security while actually acquiring and decrypting WEP / WPA1 (TKIP) / WPA2 (AES) packets.
IEEE802.11ac 80MHz compatible EyeP.A. and
IEEE802.11ax Wi-Fi 6 compatible CommView for Wi-Fi available
。 |
1 day
(10:00-18:00)
Wireshark Wireless LAN
Seminar Details

|
| Seminar name/code |
Time/venue/price example |
Overview |
Details |
[Wireshark-10]
Wireshark customization seminar for cybersecurity |

5 days (10:00-18:00)
At our training center or your site
¥27,500 per person/1 day)
|
Introduction to packet capture and trend analysis using Wireshark
Application of packet capture and trend analysis using Wireshark
Introduction to Wireshark dissector using Lua script
Malware analysis seminar using packet capture
Case study (unknown protocol analysis/decryption)
|
5 days
(10:00-18:00)
Cybersecurity Wireshark customization seminar details

|
| Seminar name/code/date |
Time, venue, price |
Overview |
Details/Application |
[VMWare-1]
Hypervisor type
Virtualization introductory seminar by VMware
|
1 day (10:00-18:00)
At our training center or your site
¥27,500 per person/1 day
|
Learn the outline and mechanism of Virtualization infrastructure through practical training on actual machines.
We will actually operate and confirm the definitions, types, and components of host-type and hypervisor-type Virtualization.
You will actually check the design, construction, and operation of a Virtualization environment by setting up a hypervisor-type Virtualization server, installing a management server, installing a guest OS, and allocating resources.
Check migration and high reliability design that utilizes Virtualization |
1 day
(10:00-18:00)
Hypervisor type
Virtualization introductory seminar
by VMware Details
 |
| Seminar name/code |
Time/venue/price example |
Overview |
Details |
[Troubleshoot-1]
Troubleshooting with commands and logs
Introductory seminar |
1 day (10:00-18:00)
At our training center or your site
¥27,500 per person/1 day
|
This is a troubleshooting seminar where you can learn how to isolate client/server/network problems and identify their causes on a layer-by-layer basis.
Learn tips and techniques for Windows/Linux commands, shell scripts, and log files (event viewer).
About Windows OS and Linux OS
Standard commands and shell scripts
Check the troubleshooting of systems and networks
that utilize log files and event viewers
in the actual environment.
Use Windows/Linux log file/event viewer and filter
Learn how to efficiently search logs by actually operating it.
Through practical training, you will learn how to check and debug program operations.
Check how to isolate troubles by OSI layer and how to identify the cause for each layer. |
1 day
(10:00-18:00)
Troubleshooting with commands and logs
Introductory seminar Details
 |
| Seminar name/code/date |
Time, venue, price |
Overview |
Details/Application |
[DNSLDAPAD-1]
DNS/LDAP/
ActiveDirectory
Introduction to name resolution
Active
Directory environment by WindowsServer
2022
Design construction operation
|
1 day (10:00-18:00)
or
by Windows Server 2022
Active Directory environment
2 days including design, construction and operation
At our training center or your site
¥27,500 per person/1 day |
We will learn the basics of today's name resolution and directory services through practice with
packet capture.
We will understand the mechanism, protocols, and packets of DNS/LDAP.
In addition, we will learn
the
mechanism, protocols, and packets of Active Directory, which is a directory system by Microsoft, and
We will understand the design, installation, and operation of ActiveDirectory through exercises. |
1 or 2 days
(10:00-18:00)
DNS/LDAP ActiveDirectory
Introduction to Name Resolution
Active Directory environment using Windows Server 2022
Design, construction and operation
Details
 |
| Seminar name/code/date |
Time, venue, price |
Overview |
Details/Application |
[VPN-1]
FortigateUTM
Firewall FW/IPSec/
SSLVPN network
Design, construction, and operation
|
1 day (10:00-18:00)
At our training center or your site
¥27,500 per person/1 day
|
By using today's firewalls for small to medium-sized businesses to protect networks, you will learn how to design, build, and operate secure networks using IPSec-based head office and branch networks (hub-spoke mesh), SSLVPN networks, smartphone connections, two-factor authentication, etc. through actual machine exercises. |
1 day
(10:00-18:00)
FW/IPSec/
SSLVPN network design
construction and operation details by FortigateUTM
 |
| Seminar name/code/date |
Time, venue, price |
Overview |
Details/Application |
[L3SW-1]
Layer 3 switch
Switching/
Routing
Highly reliable network
Design, construction, and operation
|
1 day (10:00-18:00)
At our training center or your site
¥27,500 per person/1 day
|
This is a seminar on designing, building, and operating highly reliable networks using switching and routing using L3SW.
We will introduce examples of network construction and design, as well as the best examples of network design depending on your budget and purpose.
Furthermore, we will introduce technologies for building highly reliable networks, the situations in which they are introduced, and their advantages and disadvantages.
Acquire highly reliable network design techniques through exercises using actual equipment. |
1 day
(10:00-18:00)
Layer 3 switch
Switching/
Routing
Highly reliable network
Design, construction, and operation
 |
| Seminar name/code/date |
Time, venue, price |
Overview |
Details/Application |
[IPv6-1]
IPv6 unicast multicast network design construction operation
|
1 day (10:00-18:00)
At our training center or your site
¥27,500 per person/1 day
|
This is a seminar where you will learn about the design, construction, and operation of a network in an IPv6 environment.TAG1__ Understand its structure and standards, as well as
Confirm the actual L3SW configuration and operation.
Construct an IPv6 network through packet capture. |
1 day
(10:00-18:00)
IPv6 unicast multicast network design construction operation details
 |
| Seminar name/code/date |
Time, venue, price |
Overview |
Details/Application |
[GCC-1]
Linux GCC
Introduction to C programming
|
1 day (10:00-18:00)
At our training center or your site
¥27,500 per person/1 day
|
This is a seminar to learn
GCC-compliant C programming on standard Linux. Learn
CLI application creation and debugging techniques on Linux. |
1 day
(10:00-18:00)
Introduction to Linux GCC C Programming Details
 |
| Seminar name/code/date |
Time, venue, price |
Overview |
Details/Application |
[QT-1]
QT Framework
Application Development
Introductory Seminar
|
1 day (10:00-18:00)
At our training center or your site
¥27,500 per person/1 day
|
This is an introductory seminar on
for GUI application development using the QT
(Cute) framework, which is used in
business applications using
open source such as Wireshark and VirtualBox, as well as
business applications using
copyleft license and
commercial license. |
1 day
(10:00-18:00)
QT Framework Application Development Introductory Seminar Details
 |
| Seminar name/code/date |
Time, venue, price |
Overview |
Details/Application |
[IOT-1]
RapsberryPi
Arduino
IoT development
Introductory seminar
|
1 day (10:00-18:00)
At our training center or your site
¥27,500 per person/1 day
|
This is an introductory seminar for developing IoT devices by linking RapsberryPi (Beaglebone, etc.) and
Arduino (AVI/PIC, etc.) to
. Use actual equipment |
1 day
(10:00-18:00)
RapsberryPi Aruduino Development Introductory Seminar Details
 |
Information on upcoming seminars that have ended |
|
|
Seminar environment |
|
The latest version of Wireshark and various tools
Windows11/Windows10/Kali Linux
Core i5 20 PCs with 16GB RAM SSD environment
Gigabit Ethernet LAN environment Management SW
Capture tap/Wireless LAN capture dongle
Single focal length projector/LED projector/power strip
We will carry it in and out to the venue by car. |