+ Penetration testing services and equipment sales
Ikeriri Network Service sells penetration testing and equipment. In addition to our track record in penetration testing, we have connections with a variety of small and medium-sized penetration testing equipment vendors, including supplying equipment to the Ministry of Defense and prefectural police departments. Through education and hands-on experience with these devices, we have acquired the know-how of penetration testing.
At Ikeriri Network Service, we conduct penetration tests tailored to your needs based on the specifications of the equipment and network being investigated, after concluding an NDA (non-disclosure agreement) with the customer. Although we have less manpower than major companies, we are able to perform tests and report creation at very low prices and with flexibility. We have a track record of penetration testing for medical equipment vendors, ship equipment companies, etc.
→JIS T 81001-5-1:2023” (IEC 81001-5-1:2021) compliant penetration test
Ikeriri Network Service handles penetration testing equipment from the American company Hak5 and others. Many penetration testing devices, including Hak5, do not have an official distributor system. However, we believe that there are many customers who are unable to purchase from American companies or pay by credit card. The penetration testing equipment we sell is purchased and sold on behalf of the Self-Defense Forces, prefectural police, universities, and companies based on quotations and invoices. Therefore, the selling price and time may be higher than Hak5's list price. As a general rule, we do not accept transactions with individual customers for this equipment.
   
*The penetration testing equipment we sell is a device used to learn about attacks and countermeasures on a practical network for system protection education.Actually, attacks or hacking on the external Internet violates the Unauthorized Access Act, as well as criminal and civil laws, and may be punished.
This device will be used as a complement to our cybersecurity seminars, and will be used to learn about security attacks and how to defend against them. Please confirm and agree.
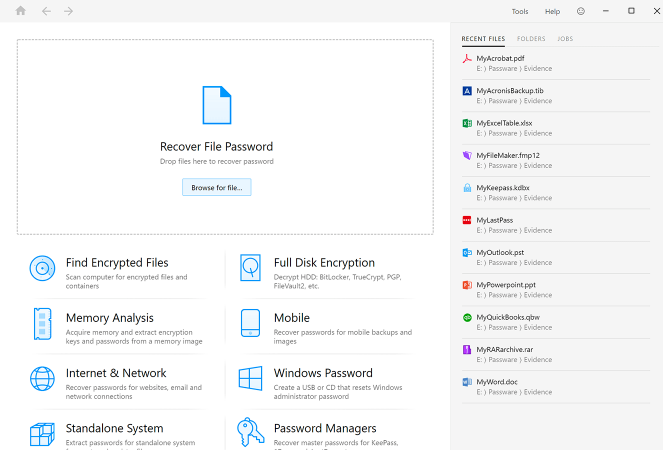 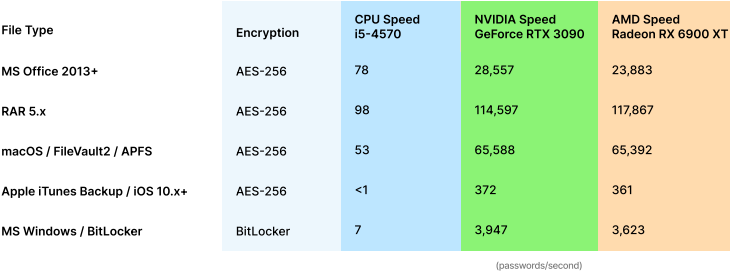
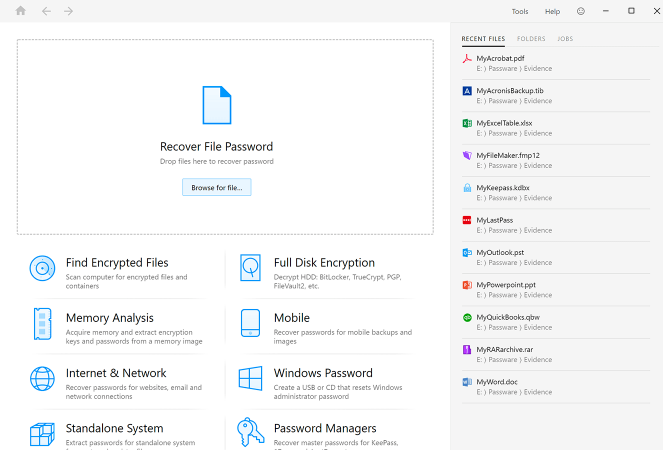
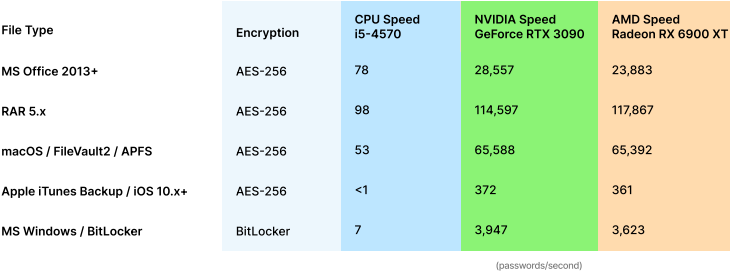
Passware Inc.PasswareKit ForensicPassword recovery Full-disk encryption and cryptocurrency recovery tool
→BadUSB Keylogger Attack AP MITM →Side-channel attacks and SDR tools →Password investigation/recovery tool
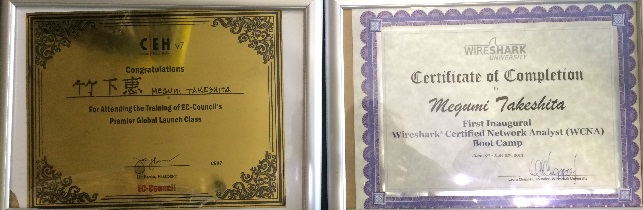
Cybersecurity Certifications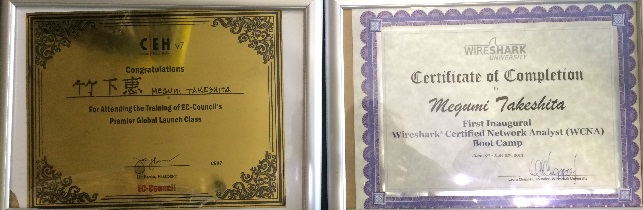
CEHv7 and WCNA certification
Ikeriri★Network Services is the only Japanese (as of 2011) who has obtained CEHv7 Certified Ethical Hacker v7, the new version of CEH, an international security qualification conducted by EC-Council, and is also holding the HackerHalted 2012 Wireshark seminar held in Miami, Florida, USA. In particular, we have a track record of holding seminars for the U.S. Forces in Japan (Okinawa). Also, regarding WiresharkExtensive track record.Cybersecurity lectures and community

In July 2017, Ikeriri Network Service Takeshita held two wireless LAN analysis workshops at Packet Hacking Village at DEFCON 25, a cybersecurity conference to be held in Las Vegas, USA at the end of July.
Basic workshop of IEEE802.11 dissection - Megumi Takeshita ikeriri (PDF)
basicworkshopofIEEE802.11dissection supplemental file (ZIP)
Ikeriri Network Services Takeshita gave a lecture at DEFCON 25, a cybersecurity conference to be held in Las Vegas, USA at the end of July. Defcon is the world's largest conference on cybersecurity.
→ DEFCON25 official→ Wall of Sheep Official → WallOfSheep DEFCON25 → Workshop introduction
Packet Capture and Cybersecurity Investigation
  
Wireshark Developer Conference CTP
2018 No. 1 in the world
Wireshark Developer Conference CTP 2016 3rd place in the world
(1) Logs of security devices such as firewalls, UTM/IDS/IPS, and log files of clients, servers, and NW devices
(2) Utilization of investigation tools such as commands/Kali/Metasploit for analyzing and isolating large amounts of logs
is also important in security investigations. Of course, it would be best if this could be used to determine the cause.
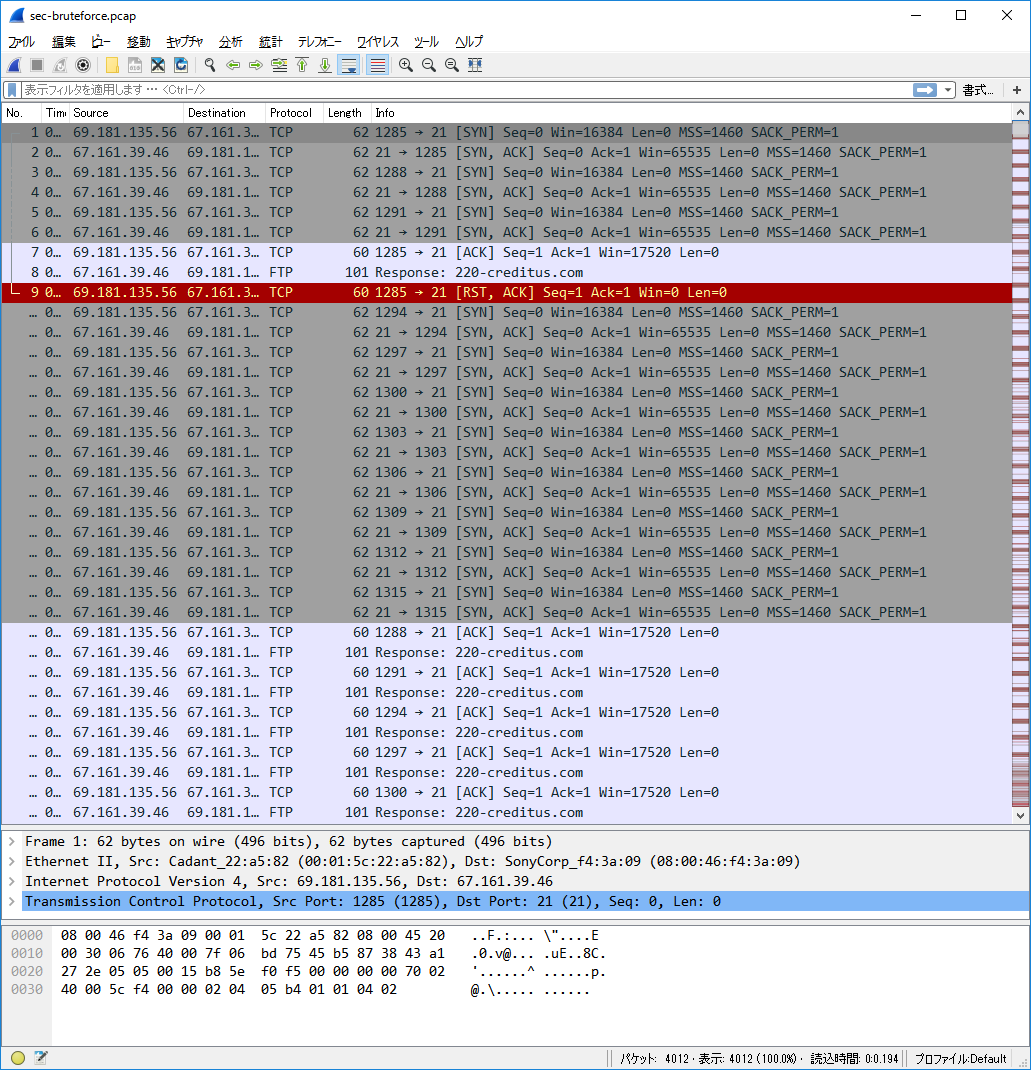
However, we provide another option for security incidents that cannot be easily resolved with these methods, where no trace is left in logs, or where the only hint is network access. Compared to methods (1) and (2), a security investigation using packet capture requires a huge amount of data and takes time and cost, but it allows you to search from a single packet. Of course, you can also leverage commercial and open source tools, automation, and AI tools. We also provide support and education, so please consider this.
 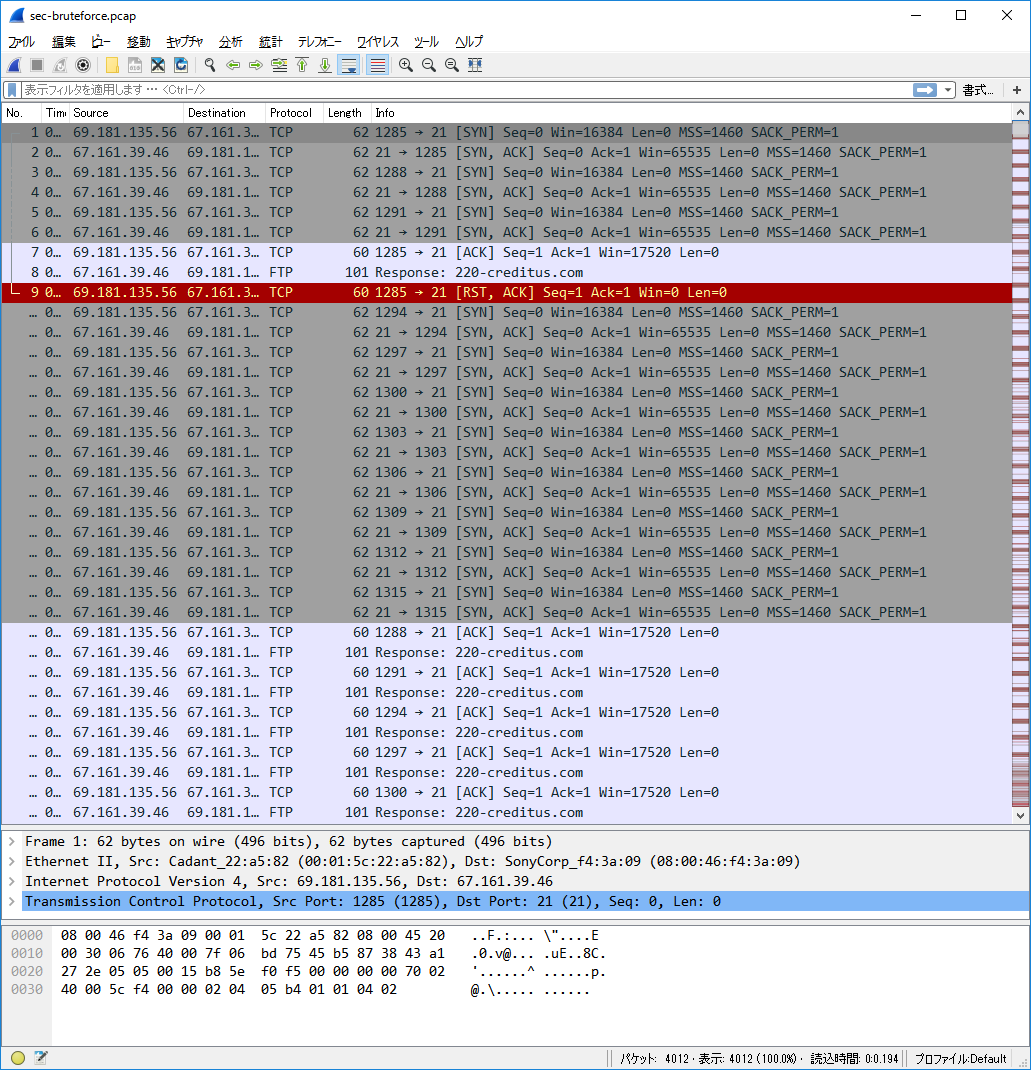
Takeshita and Kevin Mitnick of our company/Brute force attack packet example
Workflow overview
(1) Exchange of confidentiality agreement text
We will conclude a confidentiality agreement with the customer/end user as necessary.
(2) Hearing
We prepare for the investigation by interviewing the customer/end user and obtaining information about the incident overview, server environment, network environment, client, terminal, and network equipment.
(3) On-site investigation (from 1 business day)
We will bring investigation equipment (PC/wired LAN/wireless LAN capture equipment/spectrum analyzer, etc.) to the site (office/factory) and conduct a packet capture investigation for one business day (or more) at multiple locations including routers, FWs, and the relevant equipment.
*In the case of a security investigation, since it is difficult to detect an occurrence, we may visit the installation site, narrow down to a specific device, server, or subnet, and leave the equipment at the customer's site for a period of one week to one month in order to perform long-term capture.
(4) Analysis and report creation (from 2 person days)
Regarding the obtained large-capacity capture files, we use the logs of security devices such as firewalls, UTM/IDS/IPS, and log files of clients, servers, and NW devices as hints to narrow down the packets by using large-capacity packet analysis tools such as SteelCentral PacketAnalyzer to save as much time and cost as possible, and finally analyze each packet using Wireshark.
If necessary, use major security tools such as Kali/Metasploit to isolate the issue, and finally
Create a report on your findings.
(5) Investigation of cause and reporting of solutions
We will present the report to customers, end users, partner companies, and others, and investigate the cause.
As for solutions, we will do whatever we can to resolve the issue, including changing settings and device configurations, as well as contacting firmware vendors and suggesting alternative devices.
For details, please contact us inquiry(SSL).
Ikeriri Network Service handles penetration testing equipment such as side channel attack analysis and countermeasure equipment, fault injection attack analysis and countermeasure equipment, and SDR (Software Defined Radio) equipment such as semiconductor spectrum analyzers and oscilloscopes.
 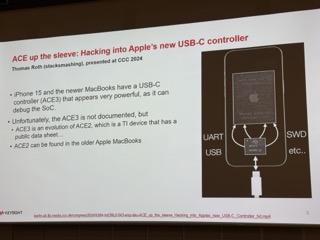
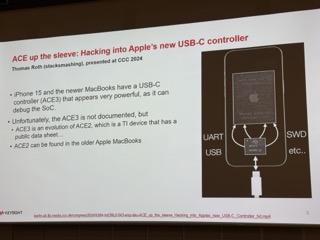
Riscure's Inspector PXI new module / iPhone USBC controller analysis
About side channel attacks
A side channel attack is an attack method that does not directly attack the internal information of a cryptographic system or other security system, but instead uses secondary information (side channel) leaked when the system executes processing to infer secret information. Cryptographic algorithms and security systems are typically assumed to be mathematically secure. However, in real system operation, secret information may be leaked through side channels such as physical information (e.g., power consumption, electromagnetic radiation, processing time). Side-channel attacks analyze these physical characteristics and infer the keys and data being processed inside the system.
About fault injection attacks
A Fault Injection Attack is a method of intentionally disrupting the normal operation of a system or device, causing abnormal behavior, and using the resulting information to attack the system. This is done on hardware and software and is used to exploit vulnerabilities in cryptographic algorithms and security systems.
 
Inspector test target module / Mark, founder of Riscure (currently Keysight)
At Ikeriri, we carry the Inspector series of pen test equipment for side channel attacks and fault injection attacks provided by Riscure of the Netherlands. →Side-channel and fault-injection attacksFor details, please contact us inquiry(SSL).
Ikeriri★Learning/Training provides seminar services at our own learning center for IT education vendors and corporate companies. For information on seminars held by our company →Seminar page.Main courses include:
As for our services for IT education vendors, we collaborate with major IT education vendor companies to plan, create, and provide training for educational content. As for services for corporations, we provide consulting, planning, management, and instructors for IT education such as computer basics, networks, TCP/IP, security, object-oriented, Java, VB.NET, vendor exams, and information processing engineer exams. We provide services that meet the needs of our customers, including practical training, test preparation, training for new employees, training for practitioners, and training for engineers. We have a track record of working with companies in a variety of industries, including the IT industry.
Ikeriri's areas of expertise include various fundamental IT technologies, networks (TCP/IP), embedded technology (C/C++ language), security, JAVA framework, .NET development, and vendor exams, as well as courses on preparing for the Ministry of Economy, Trade and Industry Information Processing Engineer Examination. training and practical trainingClick here for course examplesis. Ikeriri's published books arehereis. We have been a member of the IPv6 Popularization and Advancement Promotion Council since January 2005, and are also focusing on IPv6.
→Conference/Lecture Record
★Open seminar/seminar for customers

*JGSDF Correspondence School On-site Seminar
Ikeriri has been holding open seminars at various locations including Akihabara for the past five years.
Regularly advertise on homepages and media, and use Wireshark to capture packets and analyze dumps.
Riverbed AirPcap series Wireless LAN analysis and security investigation using Metageek Wi-Spy series
We are holding seminars related to the following. Please join us. →Seminar page
Ikeriri★Network Service also holds on-site seminars according to the needs of our customers.
We have a proven track record in government relations, including telecommunications carriers, schools, and manufacturers.
Please consider this as we will be offering it locally at a cheaper price than the Open Seminar. →Wireshark open seminar
Please feel free to contact us →ConsultationPlease.
|