|
Ikeriri Network Service handles penetration testing devices such as BadUSB devices, keyloggers, attack APs, and MiTM devices. Many penetration testing equipment vendors, including Hak5, do not have an official distributor system. However, we believe that there are many customers who are unable to purchase from American companies or pay by credit card. The penetration testing equipment we sell is purchased and sold on behalf of the Ministry of Defense, the Self-Defense Forces, prefectural police, universities, and companies based on quotations and invoices. In addition, as a general rule, we do not accept transactions with individual customers for these devices.
*The penetration testing equipment we sell is a device used to learn about attacks and countermeasures on a practical network for system protection education.Actually, attacks or hacking on the external Internet violates the Unauthorized Access Act, as well as criminal and civil laws, and may be punished.
This device will be used as a complement to our cybersecurity seminars, and will be used to learn about security attacks and how to defend against them. Please confirm and agree.
Programs and data used on devices include attack tools and malicious scripts. We do not distribute it for the purpose of attack or fraud. When using it, it may be detected by anti-spyware software or anti-virus software, or it may cause problems unintentionally. Please handle with care.
We also provide training to learn and utilize penetration testing equipment from Hak5, Keelog, and Risecure. →On-site event
We are able to host on-site events for groups as small as 5 people, so we appreciate your understanding.
Examples of Hak5 penetration testing products
Hak5's various penetration testing devices can be easily tested and inspected without the need for separate hardware, and by using the C3Cloud service, many devices can be managed and operated in an integrated manner. |
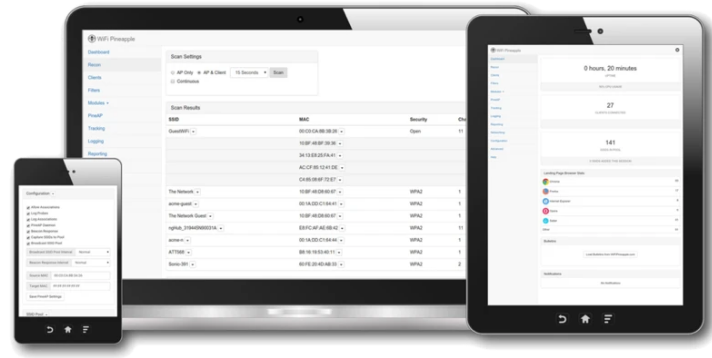
Wireless LAN Penetration Test Equipment WIFI PINEAPPLE PAGER Portable Wireless LAN Pen Test Equipment
WiFi Pineapple pager is a wireless LAN penetration test device that supports 2.4 GHz, 5 GHz, and 6 GHz tri-band wireless LAN, as well as Bluetooth and BTLE. It includes a 2000mAh battery with USB-C charging, a built-in Ethernet adapter, a color high-resolution display, 4 GB EMMC, 256 MB RAM, USB 2.0, 4 RGB LEDs, buzzer, vibration, and RTC, and can be used to test wireless LAN using the Hak5 series Ducky Script.
Equipped with the 8th generation PineAP engine, you can perform packet capture, Rogue AP (spoofed access point), Man-in-the-Middle (man-in-the-middle attacks), Deauth attacks, handshake acquisition, OSINT collection, etc. from the live dashboard. |
 |
 |
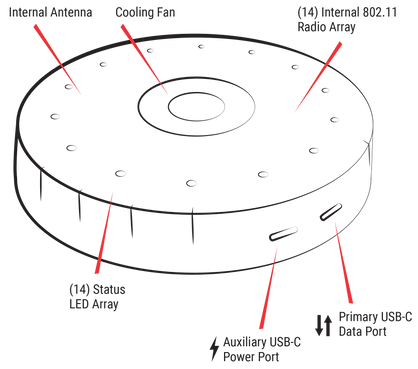
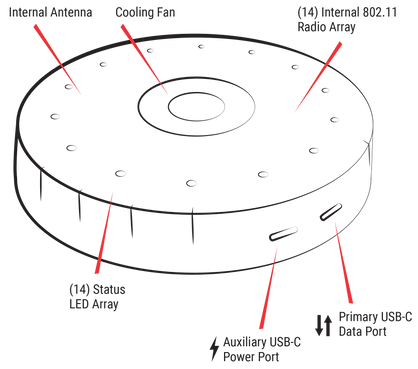
Packet capture device WiFi Coconut Captures 14 channels of 2.4GHz band simultaneously using 14 wireless LAN cards and built-in Linux
WiFi Coconut is a Linux-based wireless LAN capture device with 14 built-in wireless LAN cards. Using an open source device driver, you can simultaneously capture 14 channels of IEEE802.11b/g/n 2.4GHz band communication and save it in pcap format. The saved packets can be processed with Wireshark or other packet capture tools. The connection tool is compatible with Windows/Mac/Linux and connects via USBC. It also features an additional USBC power port and cooling fan for extended capture times. |
|
Main specifications
Built-in Linux-based OS
14 built-in wireless LAN cards
(RT2800 base driver)
USB-C PC connection port
USB-C additional power port
cooling fan
Operation LED
Cross-platform compatible
Win/Linux/Mac
Main features
2.4GHz band 14 channels simultaneous packet capture and storage in pcap format
|
|
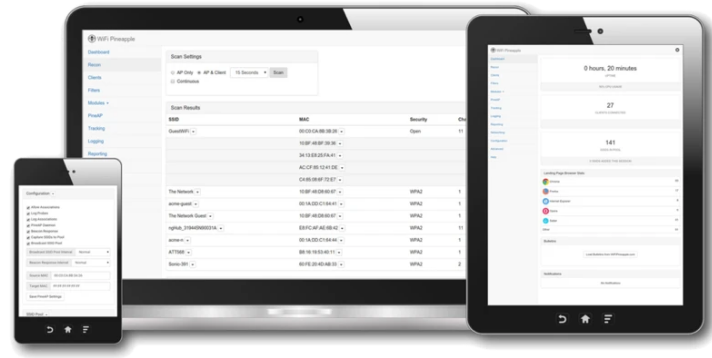
Access point for penetration testing WiFi Pineapple MARK VII BASIC
WiFi Pineapple MARK VII BASIC supports 2.4GHz IEEE802.11b/g/n and is a device that allows you to easily perform penetration tests such as wireless LAN packet capture, MITM, reconnaissance, and credential harvesting from the Web-UI using open source tools without having to prepare a separate wireless LAN card compatible with KaliLinux or aircrack-ng. |
|
Main specifications
Single-core MIPS Network SoC
256MB RAM 2GB EMMC
2.4GHz IEEE802.11b/g/n
5GHz/ac is a separate option
MK7AC Module MT7612U
AWUS036ACM MT7612U
EP-AC1605 MT7612U
3 antenna configuration
USB-C power/Ethernet port
USB2 Host port
RGB indicator
Cross-platform compatible
Win/Linux/Mac/Android/iOS
|
Main functions (common to BASIC/Enterprise)
packet capture
Access point search
Discovery of vulnerable devices
Frame insertion attacks (Deauth, etc.)
Creating a rogue AP
WPA2/3 (PSK/Enterprise) attack
MAC/SSID filter
Web interface
Cloud management compatible C2
|
Access point for penetration testing WiFi Pineapple MARK VII Enterprise
WiFi Pineapple Enterprise is compatible with 2.4GHz/5GHz IEEE802.11a/b/g/n/ac/ac wave2, and is a device that allows you to easily perform penetration tests such as wireless LAN packet capture, MITM, reconnaissance, and credential harvesting from the Web-UI using open source tools without having to prepare a separate wireless LAN card compatible with KaliLinux or aircrack-ng. |
 |
Main specifications
Quad-core ARM Network SoC
1GB RAM 4GB EMMC
2.4/5GHz IEEE802.11 a/b/g/n
ac ac wave2 compatible
8 antennas 2x2 MIMO
AC power supply
2x GigabitEthernet ports
USB3 host port
USB-C Ethernet port
4xRGB indicator
Cross-platform compatible
Win/Linux/Mac/Android/iOS |
|
Bad USB device USB Rubber Ducky A new USBC/USBA compatible model has been released.
USB Rubber Ducky is a USB memory-type penetration testing device that can perform keystroke insertion attacks. It can be programmed using a dedicated Ducky Script and can also be used as an RPA tool. Pro and Elite bundles include manuals, books, and web-based Payload Studio.
|
|
Main specifications
USB Type A interface
60MHz 32-bit CPU
Micro SD slot
Payload replay button
disassembly case
|
Main features
keystroke insertion attack
Programming with Ducky Script
Numerous payloads available
(password capture, security information dump, etc.) |
Bad USB device Bash Bunny Mark II
It is a penetration test device that has virtual Ethernet, virtual serial, virtual flash, virtual storage, and virtual keyboard on the USB device and can be treated like a Linux machine via USB-serial. BusyBunny is a device that can access connected computers and perform penetration tests such as acquiring data and installing backdoors.
Bush Bunny Mark II adds Bluetooth LE, making it possible to launch payloads from your smartphone and perform geofencing and remote triggering using Bluetooth. |
 |
Main specifications
Quad core ARM CPU
512MB RAM
8GB NAND SSD
Supports MicroSD up to 2TB
3 selector switches
multicolor led
|
Main features
Multiple payload injections (data acquisition, backdoors, system intrusion)
Virtualize keyboard and other devices
Ducky Script compatible nmap metasploit can be called
keystroke insertion attack
Payload launch and trigger via BluetoothLE
Compatible with geofencing via Bluetooth
|
MitM equipment Packet Squirrel Mark2 New model USBC power supply Supports dynamic proxy, WebUI, VPN, and Python
Packet Squirrel is a pocket-sized Ethernet MITM penetration testing device. Equipped with a variety of open source Ethernet tools, you can operate remote access, packet capture, VPN connectivity, and more from the switch. Manuals/Books and Payload Studio available with Pro and Elite bundles
|
 |
Main specifications
Inline connectable RJ-45x2
USB-A port
microUSB power supply 5V120mA
4-way payload selection switch
Status LED
push button
|
Main features
MITM attack packet capture
Tunnel NAT processing with Open VPN
DNS spoofing attack
Supports capacity expansion with USB storage
Ducky Script compatible NAT, VPN, etc.
Hak5 cloud device management C2 Cloud compatible
|
MITM equipment LAN Turtle
LAN Turtle is a USB Ethernet adapter type penetration testing device. It is possible to perform MITM attacks on connected systems using remote access tools, or to connect as a springboard. |
|
Main specifications
USB-A port
USB power supply
RJ-45 port
Micro SD port (internal)
|
Main features
Packet Capture Spoofing VPN NAT
Check and select to configure and execute main modules
(nmap/openvpn/ptunnel/dns-spoof/meterpreter etc.)
Hak5 cloud device management C2 Cloud compatible
|
Packet capture device PLUNDER BUG LAN TAP
Plunder Bug LAN TAP is a simple inline LAN tap with USB-C connection. Compatible with Windows/Mac/Linux, it can be used as an inline connection or as a regular USB-C Ethernet adapter.
|
|
Main specifications
10/100BASE-T FastEthernet
ASIX AX88772C chipset
USB-C tap and power
Compatible with Android (root required)
Compatible with Windows/Mac/Linux
|
Main features
Packet capture with inline connection (via USB-C)
Can also function as a standalone USB-C Ethernet adapter
|
Packet capture device SIGNAL OWL
SIGNAL OWL is a penetration testing device that can create a wireless LAN or Bluetooth capture/payload execution environment via USB connection. Equipped with two USB ports, you can connect GPS, SDR, and Bluetooth adapters. |
|
Main specifications
2x USB-A ports
11b/g built-in Wifi adapter
GPS/SDR/Bluetooth extension
|
Main features
Wireless LAN capture Access point detection
Supports aircrack-ng, MDK4, Kismet and other open source tools
Expand by connecting WiFi/GPS/SDR/Bluetooth adapters
Hak5 cloud device management C2 Cloud compatible
|
Screen capture equipment SCREEN CRAB
Screen Crub is a penetration testing device that tests MITM attacks on HDMI video. You can capture, stream, and save screenshots and videos from computers, monitors, and video output devices connected via HDMI.
|
|
Main specifications
HDMI port
microUSB power supply
Micro SD port
Operation LED/push button
wifi antenna
|
Main features
HDMI (FullHD 1080p) video capture and screenshots
Supports MicroSD (SDXC) for long-term recording
Storage rotation support
Online streaming compatible
Hak5 cloud device management C2 Cloud compatible
|
pen test equipment SHARK JACK
SHARK JACK is a very small, battery-operated network investigation penetration testing device. It is equipped with Linux and can send payloads compatible with Bash and DuckyScript, as well as perform network surveys and penetration tests using commands such as autossh nmap nc wget python arp-scan hping3 macchanger ngrep nping p0f tcpdump. SHARK JACK can be connected to a PC or Mac via USB-C for charging, and can be used alone by connecting to an RJ-45 port. |
|
Main specifications
RGB display LED RJ-45 connector x 1
Slide SW
USB-C port
internal battery
|
Main features
Network investigation and pentesting using tools such as autossh nmap nc wget python arp-scan hping3 macchanger ngrep nping p0f tcpdump
Executing scripts with Bash and DuckyScript
Connect and charge with PC, Mac, and Android with built-in storage and USB-C
Hak5 cloud device management C2 Cloud compatible
|
BadUSB/Keylogger KEY CROC
KEY CROC is a penetration testing device that is recognized as a HID device and can record keystrokes and perform keystroke insertion attacks. .
|
|
Main specifications
Quad core ARM CPU
512MB RAM
8GB SSD
USB-A connector
USB-A port (HID)
Built-in 2.4GHz wireless LAN
Status LED button |
Main features
Keystroke logging
New/old detection avoidance function using hardware ID clone
keystroke insertion attack
Connect via built-in WiFi
Payloads that can be pattern matched in a Ducky scripting environment
Hak5 cloud device management C2 Cloud compatible
|
pen test equipment SHARK JACK CABLE
SHARK JACK CABLE is a penetration testing device equipped with Linux and accessible via interactive serial connection, SSH and web from Android (OTG), PC and Mac via USB-C (USB UART). In addition to being able to send payloads that are compatible with Bash and DuckyScript, it is also possible to conduct network surveys and penetration tests using commands such as autossh nmap nc wget python arp-scan hping3 macchanger ngrep nping p0f tcpdump. Unlike the conventional SHARK JACK, power is supplied via USB-C. You can view real-time script results via the serial console. |
|
Main specifications
RGB display LED RJ-45 connector x 1
Slide SW
USB-C terminal (USB UART) |
Main features
Network investigation and pentesting using tools such as autossh nmap nc wget python arp-scan hping3 macchanger ngrep nping p0f tcpdump
Executing scripts with Bash and DuckyScript
Connect to PC, Mac, and Android (OTG) with USB-C
Management via serial connection (console), web, and SSH
Hak5 cloud device management C2 Cloud compatible
|
|
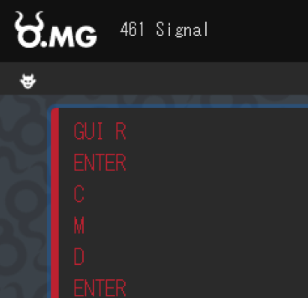
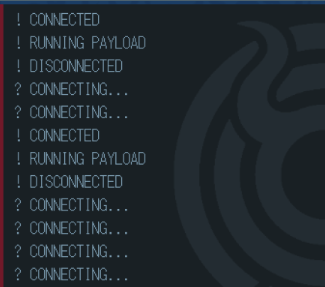
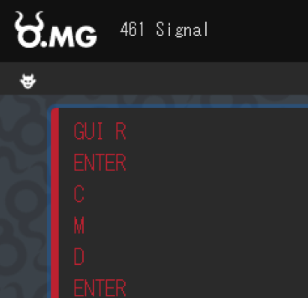
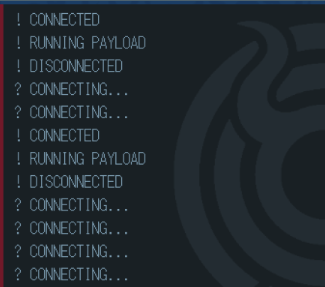
Bad USB device O.MG Basic cable and O.MG Elite cable
At first glance, O.MG CABLE looks like a USB cable (USBA/USBC to Lightning/MICRO/USB-C) for smartphone connection, but it is a Bad USB penetration test device with built-in 2.4GHz wireless LAN. The Basic version allows you to send 8 slots of DuckyScript to the connected PC. It also has a self-destruct function, geofencing using surrounding MAC addresses, and WiFi triggering functions. The O.MG Elite version uses the Convert Air Gap Exfil function to transfer not only power but also data to the O.MG cable. For example, it stores the results of receiving wireless passwords on the cable side, or executes commands such as port scans and collects the results. The AirGap Host Comms function uses O.MG's wireless interface to not only send DuckyScript but also perform two-way communication. The Networked C2 function is a function that sends and issues commands to other O.MGs using Hak5's CloudC2 service etc.
| Main features / hardware generation |
omg cable
Basic (1st generation) |
omg cable
Elite (3rd generation) |
| keystroke injection |
DuckyScript 2 |
DuckyScript 3 |
| mouse injection |
✔ |
✔ |
| Number of payload slots |
8 |
50〜300 |
| Maximum payload size |
4,000 keystrokes |
1,500,000 keystrokes |
| Maximum payload speed |
120 keys/sec |
890 keys/sec |
| self-destruct function |
✔ |
✔ |
| geofencing |
✔ |
✔ |
| WiFi trigger |
✔ |
✔ |
| Full Speed USB Hardware Keylogger |
|
✔ |
| HIDX StealthLink |
|
✔ |
| Encrypted network C2 |
|
✔ |
| Extended WiFi range |
|
✔ |
| Stealth optimized power consumption |
|
✔ |
|
 Setting requires O.MG Programmer |
Main specifications Basic or later
Built-in WiFi (2.4GHz) remote control
Customizable self-destruction
USB C to C
USB C
to Lightning
Main features
Connection via wireless LAN
Built-in web server
Android/iOS MITM
Payload insertion attack
|

Cable appearance OMG BASIC CABLE / OMG ELITE CABLE
|
 detect cable
O.MG Cable Detector
|
Keylogging feature
Multi-slot large payload
Payload injection at boot time
DuckyScript integrated
insert keystroke
USB-C smartphone and
Insert key into tablet
Geofencing MAC detection trigger
Long range WiFi trigger (2km)
scriptable web sockets
|
DuckyScript compatible payload execution from Web-UI
|
BadUSB device OMG Plug WiFi compatible PC/Mac/iOS/Android compatible DuckyScript execution tool |

OMG Plug |

OMG Programmer is required for settings such as FW update etc.
|
O.MG Plug is DuckyScript compatible with WiFi
Keystroke insertion tool.
You can dynamically change scripts and insert payloads via WiFi without having to unplug the USB port and replace the MicroSD like with USB Rubber Duck. For firmware updates, etc., use O.MG Programmer.
It comes with a strap so you can attach it to your keychain and carry it like a USB memory.
If you're familiar with the USB Rubber Duck, it's a USB Rubber Duck that can be updated remotely over WiFi. Therefore, it can be used very conveniently not only for penetration testing, but also for normal system operation work. |
Examples of Keelog keylogger products
We handle Keelog's keylogger products, including wireless LAN compatible and forensic use products.
In particular, the RS-232C connection is extremely useful for serial terminal logging and debugging as well as for purposes other than security.
*If used for employees, it is necessary to indicate the equipment and provide advance notice in the employment contract, etc.
|
Keylogger AirDrive Forensic Keylogger Pro There are also module and cable versions.
AirDrive Forensic Keylogger Pro is a small keylogger. It has built-in Wi-Fi and can be accessed not only from a PC but also from a smartphone or tablet. It also features live data streams, email reporting, timestamping, and more. |

|
Main specifications/functions
16MB encrypted storage
16,000,000 keystrokes
Transparent and undetectable by security software
Compatible with over 40 keyboards
Barcode reader compatible
WiFi HotSpot (WPA2) function
Web user interface
Report by Emai
timestamp record
live data stream |
 
|
In addition to the keylogger AirDrive Keylogger Max, there is also a KeyGrabber that can send data without wireless, and a module version and cable version.
AirDrive Keylogger Max is a keylogger with 16GB hardware encrypted memory. It has built-in WiFi and can be accessed from a PC or smart device. It also features live data streams, email reporting, timestamping capabilities, and USB flash drive recognition mode for remote or local use.
|
 |
Main specifications/functions
16GB encrypted storage
16,000,000,000 keystrokes
USB High-Speed Flash Mode
Transparent and undetectable by security software
Compatible with over 40 keyboards
Barcode reader compatible
WiFi HotSpot (WPA2) function
Web user interface
Report by Emai
timestamp record
live data stream
|
 |
Serial Logger AirDrive Serial Logger Max There is also a module version.
AirDrive Serial Logger is an RS-232C serial logging device with 16GB of encrypted storage and can be accessed from a PC or smartphone via wireless LAN. Devices with LED and push buttons and up to 115200bps can be used. It also features live data streams, email reporting, timestamping capabilities, and USB flash drive recognition mode for remote or local use. |
 |
Main specifications/functions
16GB encrypted storage
USB High-Speed Flash Mode
Asynchronous serial transfer logging
Supports reception up to 115200bps
WiFi HotSpot (WPA2) function
Web user interface
Report by Emai
timestamp record
live data stream
|
 |
Serial logger Serial Ghost TimeKeeper There is also a module version.
Serial Ghost is an RS-232C serial logging device. It has 16GB of encrypted storage and can record time stamps with a built-in battery for real-time clock. It has an LED and a push button and can use devices up to 230400bps. It has a mode where it is recognized as a USB flash drive. It is also possible to send and receive commands using the virtual COM mode function. |
 |
Main specifications/functions
16GB encrypted storage
USB High-Speed Flash Mode
Asynchronous serial transfer logging
Communication using virtual COM mode
Supports sending and receiving up to 230400bps
battery backup
timestamp record
|
 |
| USBKill is an integrated USB memory that applies an electrical load to the USB interface to test the interface for malfunctions and stress tests. V4 has stronger discharge capacity and improved stability, has a built-in rechargeable battery, and also allows for "offline attacks". Offline mode bypasses all known USB-C and Lightning (Apple/iPhone) security protocols and allows you to test smartphones and modern hardware. |
 |
USB Penetration Test Equipment USB Kill Series
BASIC
• V4 framework • Supports offline attacks • Unlimited usage • Multi-pulse attack • Magnetic trigger (activated by magnetic switch)
PRO
• V4 framework • Supports offline attacks • Unlimited usage • Single pulse attack • Continuous pulse attack • Wireless function • Magnetic trigger • Remote control trigger (remote control activation) • Compatible with smartphone control app • Timer attack
CLASSIC
• V4 framework • Classic “Plug & Zap” mode only • Unlimited usage
We also offer Basic/Pro kits and Tactical kits for industrial use as kit series that add adapters and testers to these products. |
Please feel free to contact us →ConsultationPlease.
|
|
|