|
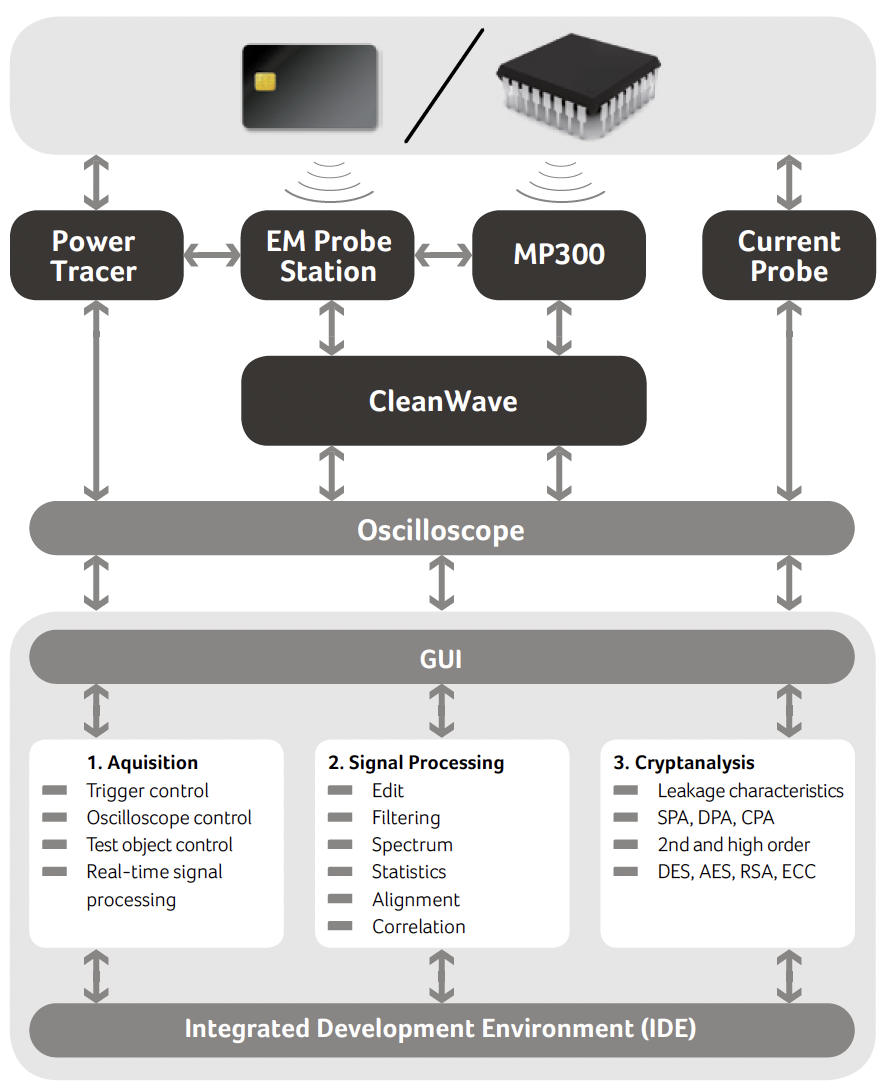
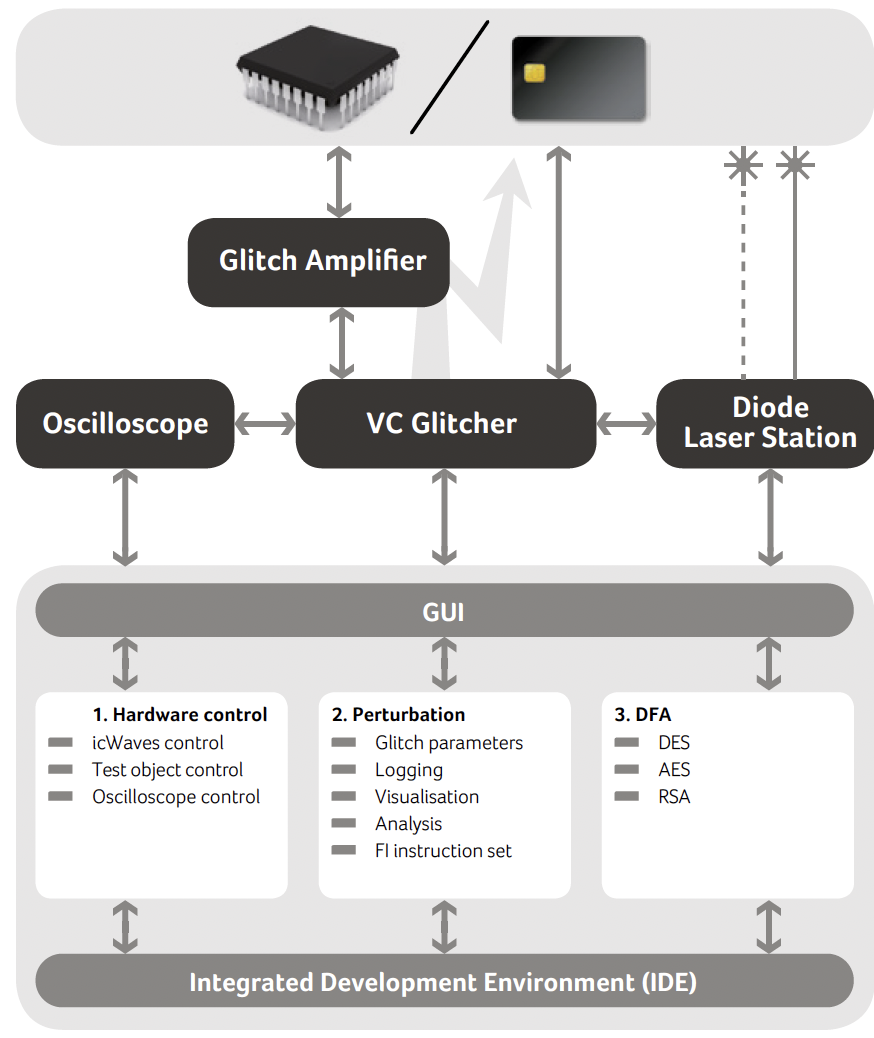
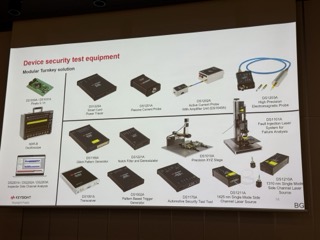
Ikeriri Network Service handles penetration testing equipment such as side channel attack analysis and countermeasure equipment, fault injection attack analysis and countermeasure equipment, and SDR (Software Defined Radio) equipment such as semiconductor spectrum analyzers and oscilloscopes.
  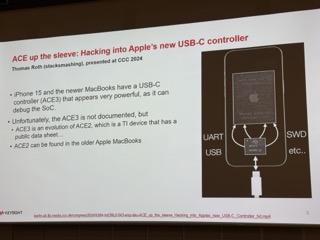
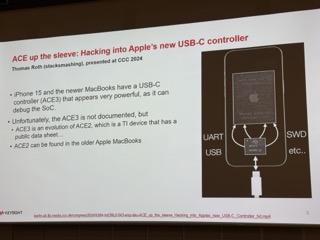
Riscure (currently Keysight) founder Mark / PXI new module / iPhone USBC controller analysis
About side channel attacks
A side channel attack is an attack method that does not directly attack the internal information of a cryptographic system or other security system, but instead uses secondary information (side channel) leaked when the system executes processing to infer secret information.
Cryptographic algorithms and security systems are typically assumed to be mathematically secure. However, in real system operation, secret information may be leaked through side channels such as physical information (e.g., power consumption, electromagnetic radiation, processing time). Side-channel attacks analyze these physical characteristics and infer the keys and data being processed inside the system.
Typical types of side channel attacks
1. Power consumption analysis (Power Analysis)
- Summary: Observe fluctuations in power consumption of encryption devices and infer encryption keys and secret information.
- Method:
- Simple Power Analysis (SPA):
- Directly observe power consumption waveforms and identify key processing patterns.
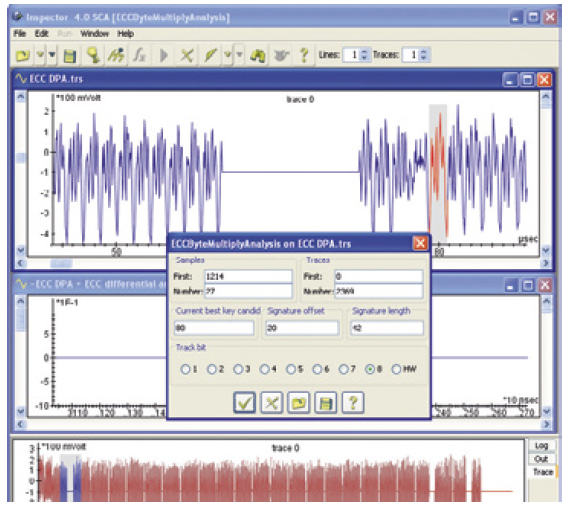
- Differential Power Analysis (DPA):
- Infer the encryption key using statistical fluctuations in power consumption.
- Target: smart cards, IoT devices, cryptographic modules.
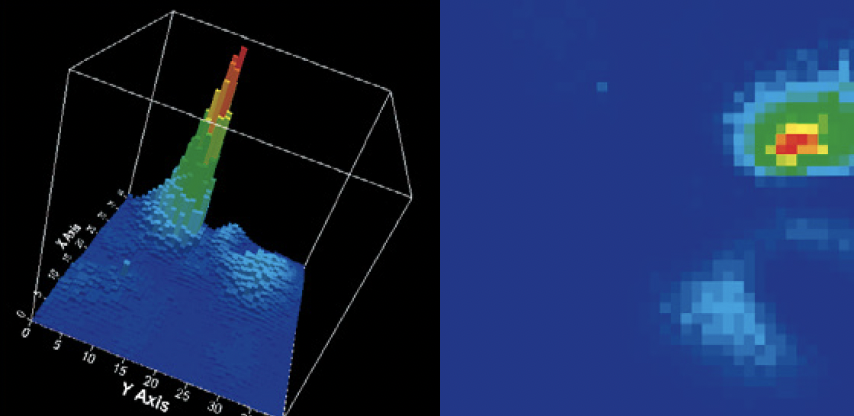
2. Electromagnetic Analysis (EMA)
- Overview: Measures electromagnetic waves emitted by devices during operation and restores processing details.
- Method:
- Infer cryptographic processing and key information from differences in radiation patterns.
- Target: Electromagnetic waves leaking from device casings and cables.
3. Time analysis (Timing Attack)
- Overview: Observe differences in processing time and infer internal processing content and key information.
- Example: The number of conditional branches and loops in a cryptographic algorithm affects processing time.
- Target: Encryption algorithms in general (e.g. RSA, ECDSA).
4. Cache Timing Attack
- Summary: Analyzes processor cache memory usage and deduces keys used for encryption.
- Example: Analyzing the cache access pattern of the AES cryptographic algorithm on the processor.
5. Acoustic Analysis
- Overview: Analyze the sound waves generated while the device is operating and deduce keys and data.
- Examples: keyboard typing sounds and hard disk drive sounds.
6. Optical Analysis
- Overview: Observe the blinking of the device's LED and changes in light intensity to infer the data processing content.
- Example: The blinking pattern of the router's LEDs indicates the content of the data communication.
7. Temperature/radiation attack
- Overview: Measure changes in device surface temperature and thermal radiation to estimate processing status.
- Target: High performance devices and large systems.
The following methods can be used to prevent side channel attacks.
1. Reducing physical leakage
- Apply shielding to the device housing (blocking electromagnetic waves and sound waves).
- Inject noise or random data to make measurements difficult.
2. Countermeasures at algorithm level
- Keep the processing time constant (preventing timing attacks).
- Randomize part of the encryption key to nullify fluctuations in power consumption and electromagnetic waves.
3. Improved hardware design
- Adopts a leak-resistant design (e.g. hardware cryptographic module).
- Circuit design that reduces power consumption and electromagnetic waves.
4. Monitoring and evaluation
- Deploy sensors and monitoring systems to detect side-channel attack attempts.
- Assess leaks with regular penetration tests. |